vRealize Automation
 Written by Sam McGeown
on 25/6/2021
Written by Sam McGeown
on 25/6/2021Published under vRealize Automation and vRealize Orchestrator
 I was doing some testing with adding an external vRealize Orchestrator 8.4 endpoint to vRealize Automation Code Stream 8.4, and it turns out there’s a redirect that happens with the vRO 8.4 appliance that makes the endpoint validation fail. When you enter the URL and click ACCEPT CERTIFICATE the UI will throw an error: Server error on getting certificates.
Http failure response for https://<vRA FQDN>/codestream/api/endpoint-certificate?url=https://<vRO FQDN>: 400 Bad Request
Error getting certificates!
I was doing some testing with adding an external vRealize Orchestrator 8.4 endpoint to vRealize Automation Code Stream 8.4, and it turns out there’s a redirect that happens with the vRO 8.4 appliance that makes the endpoint validation fail. When you enter the URL and click ACCEPT CERTIFICATE the UI will throw an error: Server error on getting certificates.
Http failure response for https://<vRA FQDN>/codestream/api/endpoint-certificate?url=https://<vRO FQDN>: 400 Bad Request
Error getting certificates! Written by Simon Eady
on 18/3/2021
Written by Simon Eady
on 18/3/2021Published under vRealize Automation
 Integrating vROps with vRA 8 using Workspace One Auth Source Product Version - vRealize Automation 8.x Why integrate vROps with vRA 8? vRealize Automation can work with vRealize Operations Manager to perform advanced workload placement, provide deployment health and virtual machine metrics, and display pricing.
So what is the problem? When configuring the integration, you will input the vROps URL and it will also ask you to input a username and password of the service account you wish to use.
Integrating vROps with vRA 8 using Workspace One Auth Source Product Version - vRealize Automation 8.x Why integrate vROps with vRA 8? vRealize Automation can work with vRealize Operations Manager to perform advanced workload placement, provide deployment health and virtual machine metrics, and display pricing.
So what is the problem? When configuring the integration, you will input the vROps URL and it will also ask you to input a username and password of the service account you wish to use. Written by Simon Eady
on 21/2/2021
Written by Simon Eady
on 21/2/2021Published under vRealize Automation
 Why use Content Libraries with vRA 8 Product Version - vRealize Automation 8.x What are vSphere Content Libraries? A content library stores and manages content in the form of library items. A single library item can consist of one file or multiple files. For example, the OVF template is a set of files (.ovf, .vmdk, and .mf). When you upload an OVF template to the library, you upload the entire set of files, but the result is a single library item of the OVF Template type.
Why use Content Libraries with vRA 8 Product Version - vRealize Automation 8.x What are vSphere Content Libraries? A content library stores and manages content in the form of library items. A single library item can consist of one file or multiple files. For example, the OVF template is a set of files (.ovf, .vmdk, and .mf). When you upload an OVF template to the library, you upload the entire set of files, but the result is a single library item of the OVF Template type. Written by Sam McGeown
on 4/11/2020
Written by Sam McGeown
on 4/11/2020Published under vRealize Automation
 To generate a basic authentication header from a username and password in Code Stream you could use a CI task and execute echo -n username:password | base64 in the shell then export the result for use later on. A more repeatable way is to create a Custom Integration that takes the two inputs, and returns the encoded header as an output.
To create the Custom Integration:
Create a new Custom Integration named “Create Basic Authentication Header” Select the Runtime - the examples below are shell and python3 respectively Replace the placeholder code with the example from below Save and version the Custom Integration, ensuring you eanble the “Release Version” toggle Creating the Custom Integration To use the Custom Integration in a pipeline:
To generate a basic authentication header from a username and password in Code Stream you could use a CI task and execute echo -n username:password | base64 in the shell then export the result for use later on. A more repeatable way is to create a Custom Integration that takes the two inputs, and returns the encoded header as an output.
To create the Custom Integration:
Create a new Custom Integration named “Create Basic Authentication Header” Select the Runtime - the examples below are shell and python3 respectively Replace the placeholder code with the example from below Save and version the Custom Integration, ensuring you eanble the “Release Version” toggle Creating the Custom Integration To use the Custom Integration in a pipeline: Written by Simon Eady
on 29/7/2019
Written by Simon Eady
on 29/7/2019 I have been working with VMware Cloud Foundation recently and while for the most part things went well there were occasions where challenges were encountered which made the delivery to the customer all the more trickier than expected.
This article is a list of observations and things to most definitely check or watch out for when delivering a VCF project.
We were working with VCF version 3.7.2 (yes I am aware 3.
I have been working with VMware Cloud Foundation recently and while for the most part things went well there were occasions where challenges were encountered which made the delivery to the customer all the more trickier than expected.
This article is a list of observations and things to most definitely check or watch out for when delivering a VCF project.
We were working with VCF version 3.7.2 (yes I am aware 3. Written by Simon Eady
on 5/4/2019
Written by Simon Eady
on 5/4/2019Published under VMware and vRealize Automation
 I recently upgraded an instance of vRA from 7.2 to 7.5 and rather than do it the manual way I used VMware’s vRealize LifeCycle Manager (version 2.0 update 3).
Everything was going great and according to plan, the vRLCM pre-requisites checker made short work of all of the checks you need to do before you start an upgrade of vRA. You can see below vRLCM does a great job of keeping you informed of the current progress and in a really elegant way.
I recently upgraded an instance of vRA from 7.2 to 7.5 and rather than do it the manual way I used VMware’s vRealize LifeCycle Manager (version 2.0 update 3).
Everything was going great and according to plan, the vRLCM pre-requisites checker made short work of all of the checks you need to do before you start an upgrade of vRA. You can see below vRLCM does a great job of keeping you informed of the current progress and in a really elegant way. Written by Sam McGeown
on 26/3/2018
Written by Sam McGeown
on 26/3/2018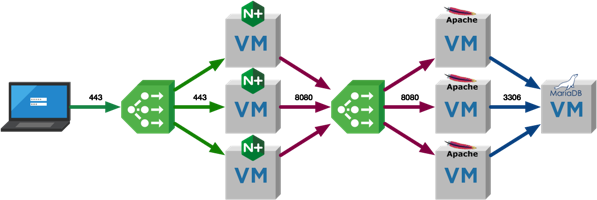 One question I’m asked quite a lot is what I use for a 3-tier application when I’m testing things like NSX micro-segmentation with vRealize Automation. The simple answer is that I used to make something up as I went along, deploying components by hand and generally repeating myself a lot. I had some cut/paste commands in my note application that sped things up a little, but nothing that developed. I’ve been meaning to rectify this for a while, and this is the result!
One question I’m asked quite a lot is what I use for a 3-tier application when I’m testing things like NSX micro-segmentation with vRealize Automation. The simple answer is that I used to make something up as I went along, deploying components by hand and generally repeating myself a lot. I had some cut/paste commands in my note application that sped things up a little, but nothing that developed. I’ve been meaning to rectify this for a while, and this is the result! Written by Sam McGeown
on 2/2/2018
Written by Sam McGeown
on 2/2/2018Published under VMware and vRealize Automation
 Just a quick post today, as I was working with a customer recently and we were trying to retrieve the Custom Properties assigned to a vRealize Automation 7.3 deployed Virtual Machine, similar to the one in the image below. It’s not as intuitive as you’d like it to be because of the split between IaaS APIs and Cafe APIs. Below you can see I’ve deployed a simple CentOS blueprint with a custom property at the Blueprint level (called “BlueprintLevel” with a value of “CustomProperty”) and a custom property at the VM level (called “CustomProperty” and a value of “Test123”).
Just a quick post today, as I was working with a customer recently and we were trying to retrieve the Custom Properties assigned to a vRealize Automation 7.3 deployed Virtual Machine, similar to the one in the image below. It’s not as intuitive as you’d like it to be because of the split between IaaS APIs and Cafe APIs. Below you can see I’ve deployed a simple CentOS blueprint with a custom property at the Blueprint level (called “BlueprintLevel” with a value of “CustomProperty”) and a custom property at the VM level (called “CustomProperty” and a value of “Test123”). Written by Sam McGeown
on 19/1/2018
Written by Sam McGeown
on 19/1/2018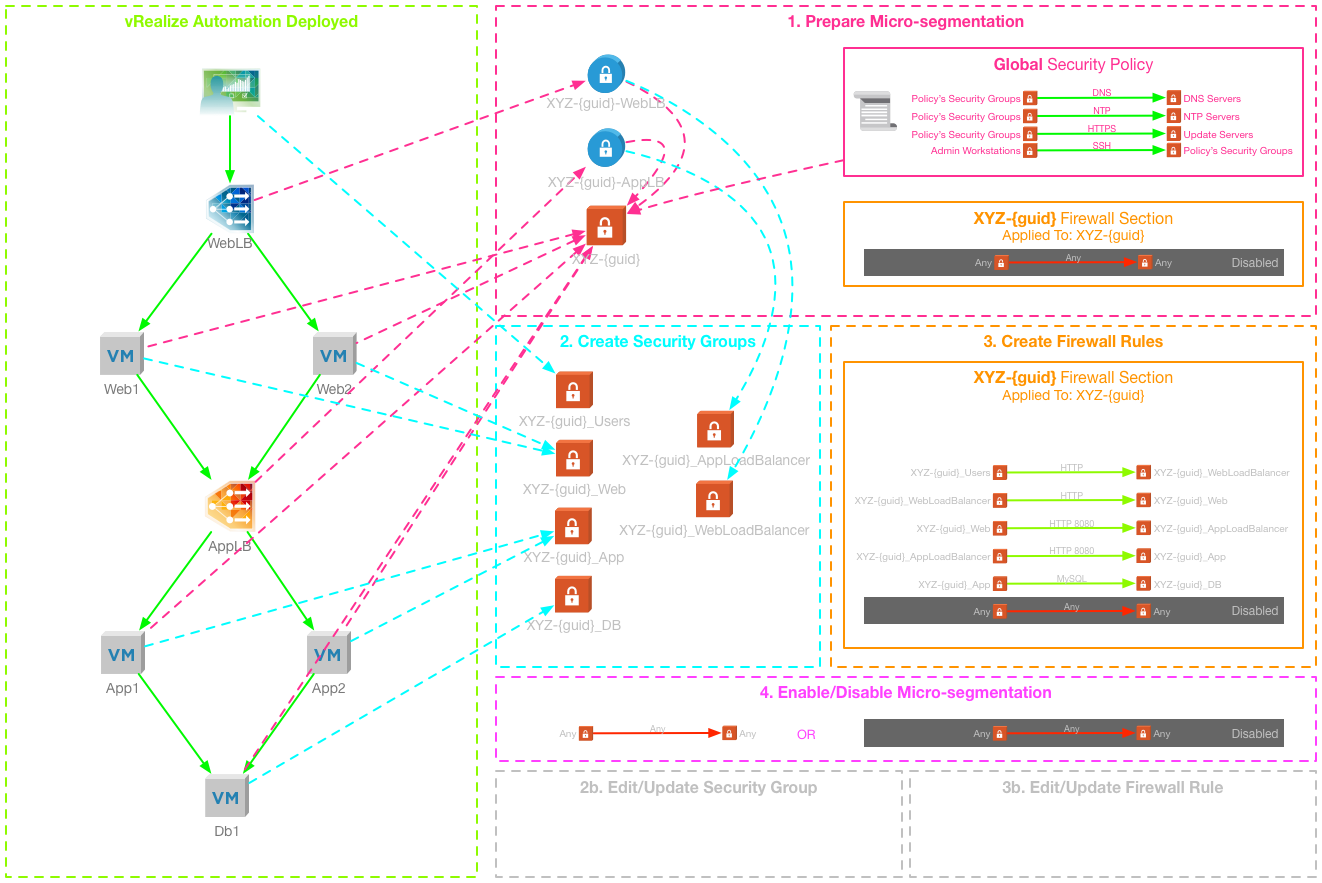 vRealize Automation and NSX integration has introduced the ability to deploy multi-tiered applications with network services included. The current integration also enables a method to deploy micro-segmentation out of the box, based on dynamic Security Group membership and the Service Composer. This method does have some limitations, and can be inflexible for the on-going management of deployed applications. It requires in-depth knowledge and understanding of NSX and the Distributed Firewall, as well as access to the Networking and Security manager that is hosted by vCenter Server.
vRealize Automation and NSX integration has introduced the ability to deploy multi-tiered applications with network services included. The current integration also enables a method to deploy micro-segmentation out of the box, based on dynamic Security Group membership and the Service Composer. This method does have some limitations, and can be inflexible for the on-going management of deployed applications. It requires in-depth knowledge and understanding of NSX and the Distributed Firewall, as well as access to the Networking and Security manager that is hosted by vCenter Server. Written by Simon Eady
on 22/9/2017
Written by Simon Eady
on 22/9/2017Published under vRealize Automation and vRealize Operations
In this episode, Sunny gave us a deep dive into the WLP and WLB features of vROps.
We were also joined by a special guest, Jad El-Zein who gave us a great insight into how vRA utilises vROps for initial placement of freshly provisioned VMs
We would highly appreciate it if you could spend 30 seconds to fill up this quick and simple survey to provide us your feedback. You can also request topics of your choice through this survey.
